Exploring GPO Loopback Processing
First of all, what is GPO loopback processing?
It's a way of deploying user GPO settings to a machine account.
Ok, so what's that mean?
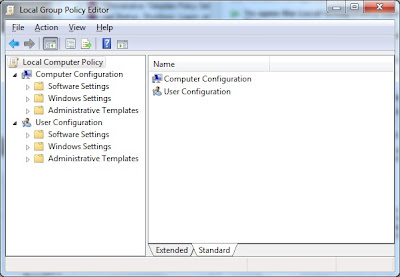
Inside gpedit.msc are two groups, users and computers:
Computer settings are things that affect the computer, i.e. stuff you can do without being logged on so things like the machines shutdown polices, certain 'hands off' software installs and logon text.
On occasion though, you might want user policies to apply to anyone who logs onto those computers, for example, if you have loan laptops or kiosk type machines then you may well want a default set of user policies to be pushed out to any user who logs on and this is where GPO Loopback processing comes in.
It's a nice feature to allow those default user policies to deployed to a machine no matter who logs in.
And THAT is really all it's meant to do but several times now I've seen it abused in environments where administration rights are split between different teams. Active Directory very much allows for delegated administration rights but it's not so good for allowing delegated access when the users are in Corporate OU's and the computers that use are in the delegated OU's - a situation I recently had to try to unravel.
What the OU admins had decided to do was to use loop back processing so that any users using computers they owned got the policies they wanted them to have - something of a nightmare to unravel when their problems because of the corporate user policies + the loopback processing policies.
Of course, a lot of this boils down to politics rather than technical issue but if you ever do find yourself in that sort of situation do be careful with how you apply policies and if possible make sure that user policies are deployed to users rather than succumbing to the loopback processing 'workaround'.
Subscribe to Ramblings of a Sysadmin
Get the latest posts delivered right to your inbox