Just how good is IISCrypto?
I've played around with IIS Crypto a fair bit, for those who don't know it, it's a freeware application that can make changes to the registry to restrict the protocols that are used by IIS in order to secure it and avoid the SSL sites being affected by vulnerabilities such as poodle, drown and so on.
I wondered just how good an application is it?
Well, after some testing, it's pretty damn good.
I had some free credit at Azure so I decided to spin up an IIS VM and run a the testing against it to see how it fairs out of the box.
The test I ran was a very simple test, I spun a Windows 2012 R2 box up at Azure, installed IIS and connected to it over it's IP address to do basic validation. I then set up a DNS pointer to it and grabbed an SSL cert from and once all configured, the default IIS page was available over SSL.
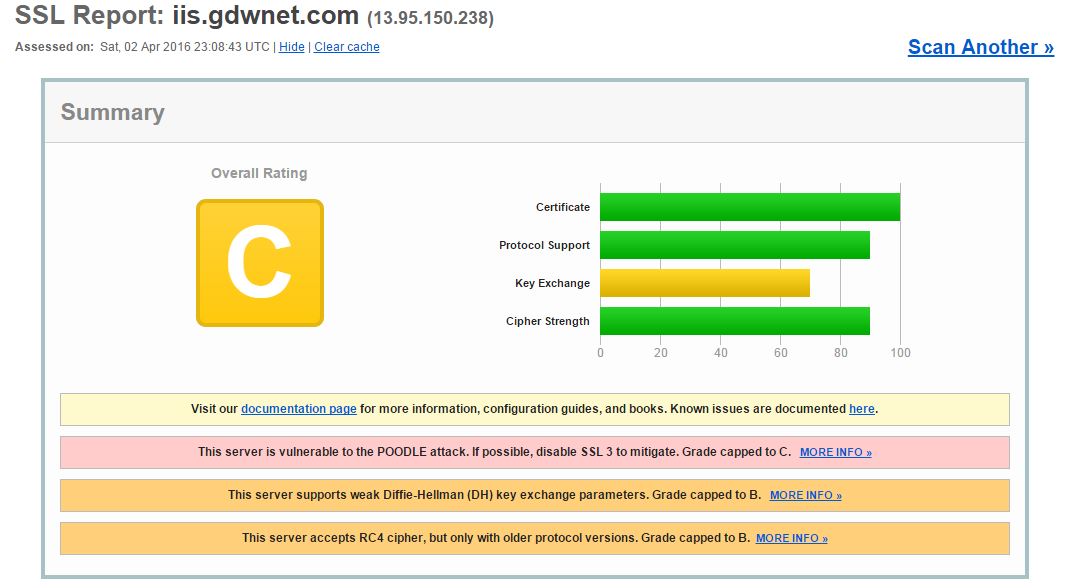
So, out of the box, with SSL enabled, how does IIS fare according to Qualsys?
Actually, not too badly:
It rated a "C" with the server being vulnerable to Poodle.
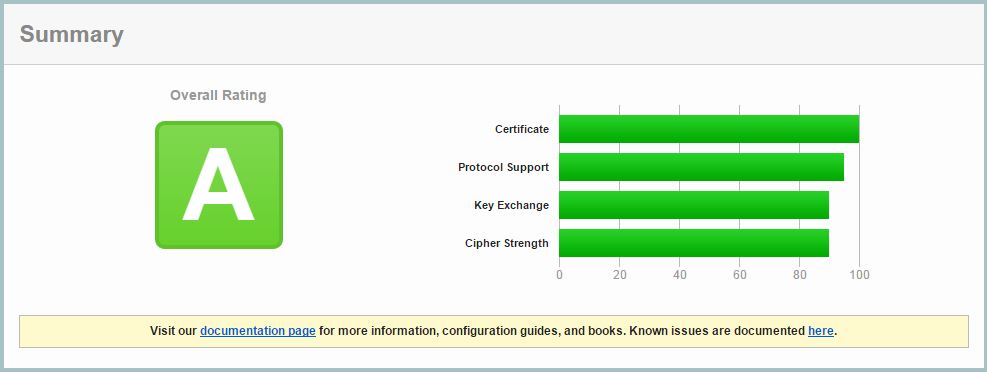
Running the IIS Crypto tool and selecting "Best Practices" removed a whole list of ciphers and protocols. A reboot was required which was slightly annoying but as this changes the registry it's understandable.
A quick test on Qualsys again and we get a nice 'A' rating:
An 'A' is good but it's not an 'A+' which I'd have liked to have seen, unfortunately, I didn't have the time to do any further testing but a quick google and I did see an article from Scott Helme about adding in the "strict transport security" header into IIS
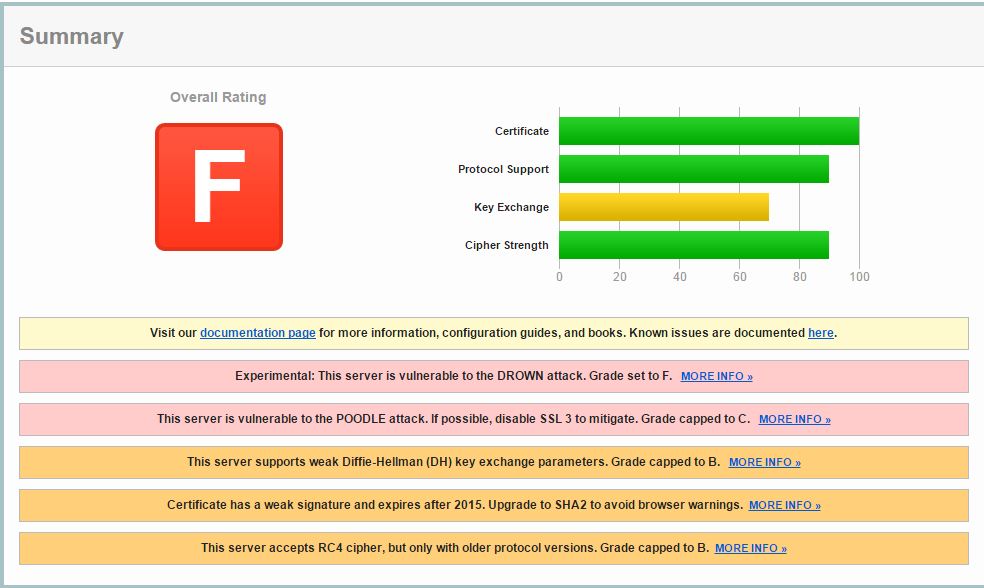
This is all very straight forward and simple for a single IIS site but if you have multiple sites on the same server then you're going to need to test each and every site as multiple sites are a key requirement to make a server vulnerable to drown, add in allowing SSL 2 or 3, RC4 as a cipher and still using SHA-1 certs and you get........
Avoid the 'F' grading! Look after your protocols no matter where the web server is hosted and regularly test the rating of the site.
Subscribe to Ramblings of a Sysadmin
Get the latest posts delivered right to your inbox